Motadata

Mobile alerting with tracking & escalation for Motadata
![]() Why Enterprise Alert
Why Enterprise Alert
Motadata is a network, database, server and application monitor that uses a wide variety of built in policies to alert on incidents that happen. Performance monitors are easy to configure, and notifications channels are configured with just a few clicks. Enterprise Alert ensures that all on duty members receive, acknowledge and resolve critical alerts, all from their smartphones. With persistent notifications and escalation chains there will never be a critical alert that goes unattended. Enterprise Alert also offers ad-hoc collaboration between team members for each alert, so Subject Matter Experts can be looped in to help resolve issues.
![]() How it Works
How it Works
Policy actions report incident data to Enterprise Alert using email as the delivery method. Enterprise Alert receives these emails and alerts all on-duty team members via push, SMS and voice notifications.
![]() Integration Capabilities
Integration Capabilities
- Forwards Motadata incident information to Enterprise Alert for mobile alerting
- Uses SMTP email to connect to your Enterprise Alert team
- Staff can acknowledge and take ownership for critical events that occur
- Communicate within an alert to address a problem
- Alerts are escalated in case of no response
- On-call scheduling to alert the right people at the right time
![]() Scenarios
Scenarios
- Network Monitoring
- Database Monitoring
- Server Monitoring
- Application Monitoring
How to Integrate
In our example we are using Motadata to ping critical servers in our infrastructure. Policy actions will be put in place to send an email alert to the Enterprise Alert team.
Integration Steps
For our example we will assume that your network topology has all been discovered and there are current monitors in place. We will assign a new action to the alert monitor which will forward an email to the operation team.
- Edit an existing monitor. We will use PING. Select Alerts > Monitor Alerts and search for Ping. The Ping Availability monitor will display. Click edit,
- Once the monitor loads in the Unreachable section click New under actions
- Populate the action as shown below.
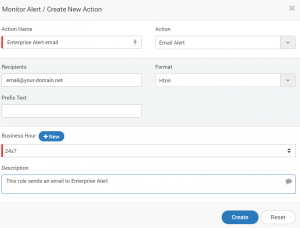
- Click Create at the bottom of the screen.
- That’s It! The next time this monitor triggers an email will be sent to Enterprise alert and routed to the designated team.
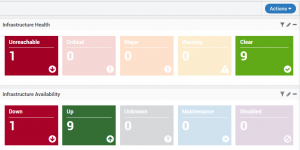
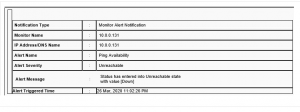
Here is an example of the monitors triggering in the Motadata dashboard.
Emails are typically received like this:
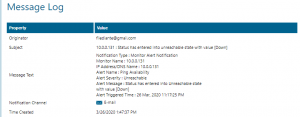
The email that is received in Enterprise Alert shows up under Message Log > Incoming Messages
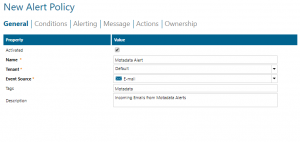
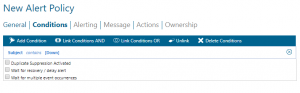
- Now let’s create an alert policy within Enterprise Alert. The following screenshots show an example of a basic policy that is triggered when the subject lines contain [Down]. When this policy is triggered it will be routed to the IT Operations team and notify each member via push, SMS, Voice and Email, depending on their notification profile.
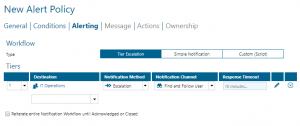
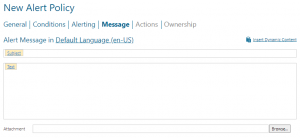
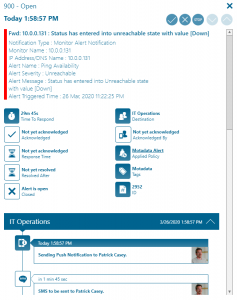
Enterprise Alert parses this email and identifies the status of [Down] and triggers the policy to alert the IT Operations team.
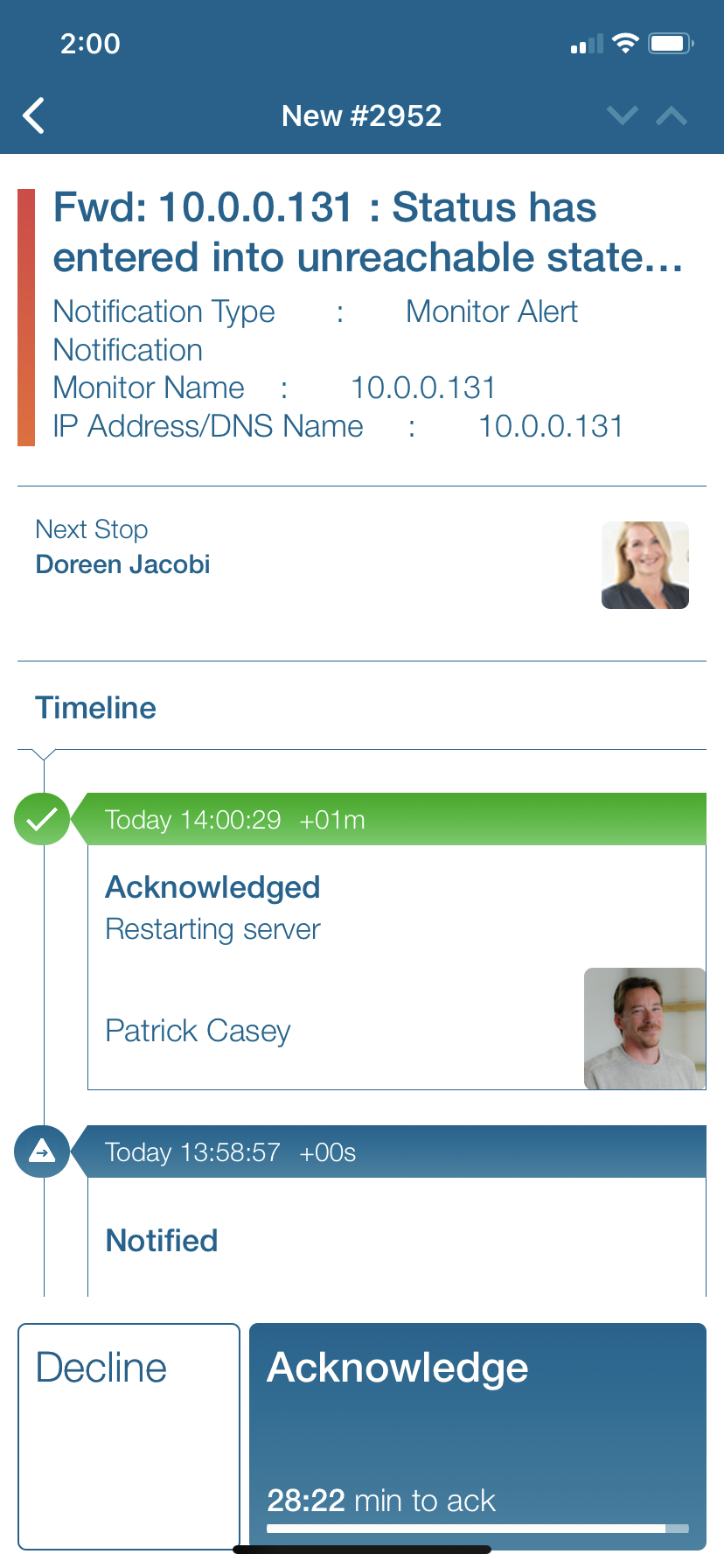
Notifications within the Enterprise Alert mobile app
Enterprise Alert comes complete with a mobile app allowing for all critical alert details to be seen from anywhere. Users can acknowledge and take ownership of alerts and with remote actions, even resolve them. Team members collaborate with their peers so that even if an on-call person is not the SME, that person is easily within reach via voice call, text or email.
A centralized Alert Center can be viewed from the web portal. All alerts, whether active, overdue or closed are visible to EA admins. Ownership and even delegation is as easy as drag-and-dropping the alert to the person/team.